Effectively and efficiently onboard your specialty patients
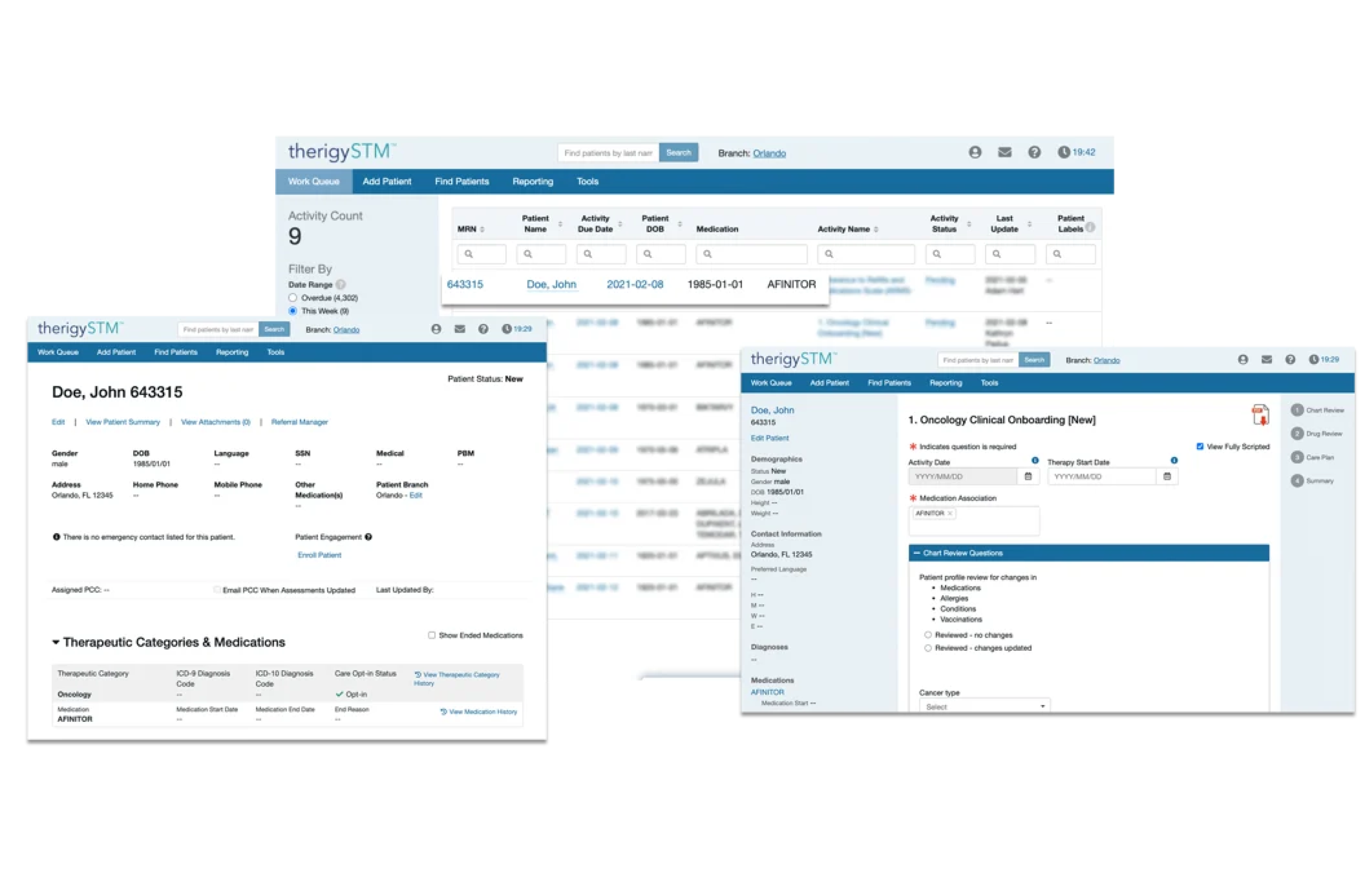
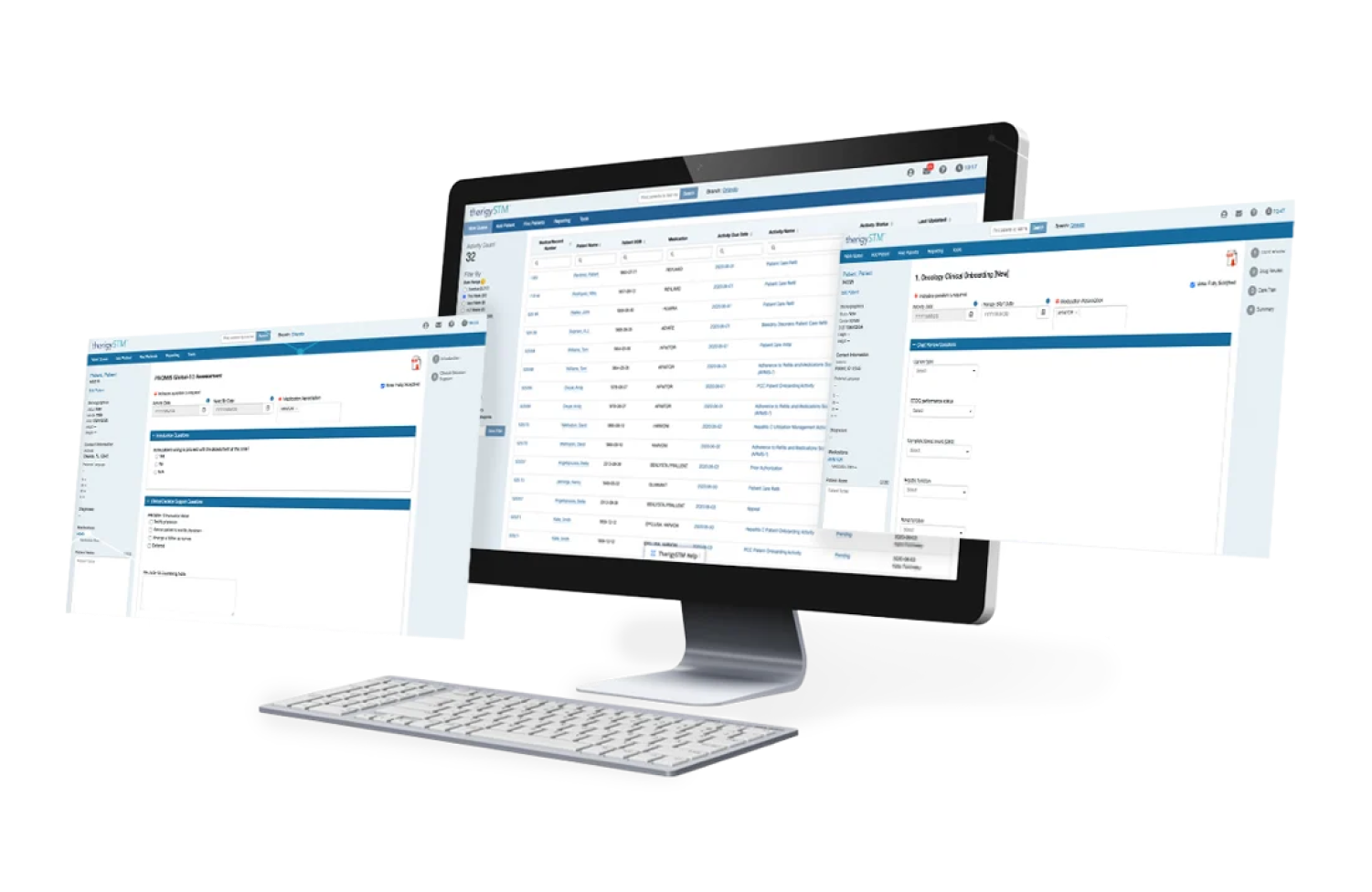
Onboarding Patients
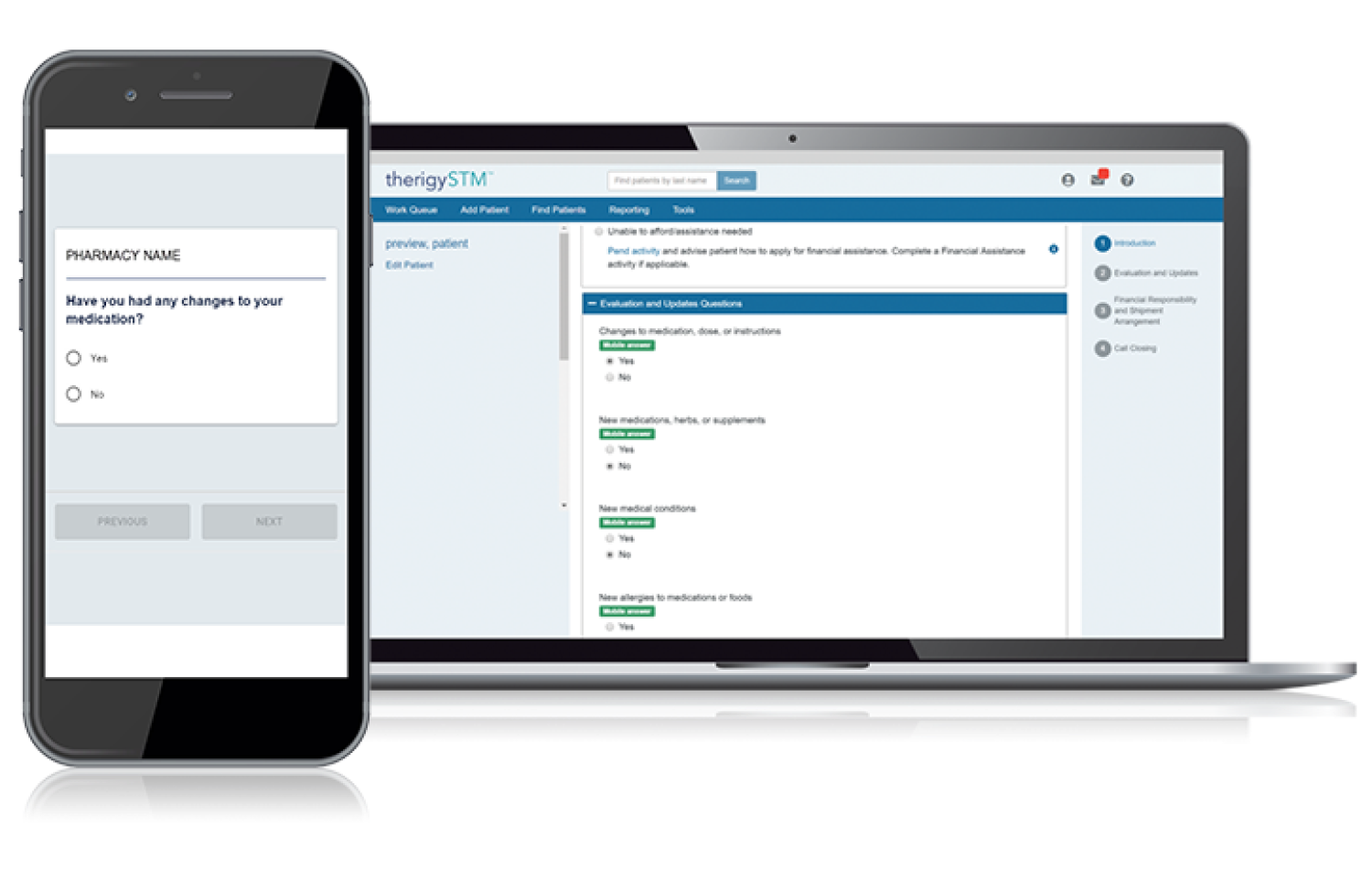
With TherigySTM, you have flexible options to add patients manually or automatically from your EHR, pharmacy management system, and/or dispensing system. TherigySTM integrates with the top systems in the country to increase your team’s productivity with interoperability, which saves $48k in annual operational savings on average.